IT, Cybersecurity & Cloud Insights
Practical guidance from the team that runs Chicago's IT environments, written for business owners and IT decision-makers.
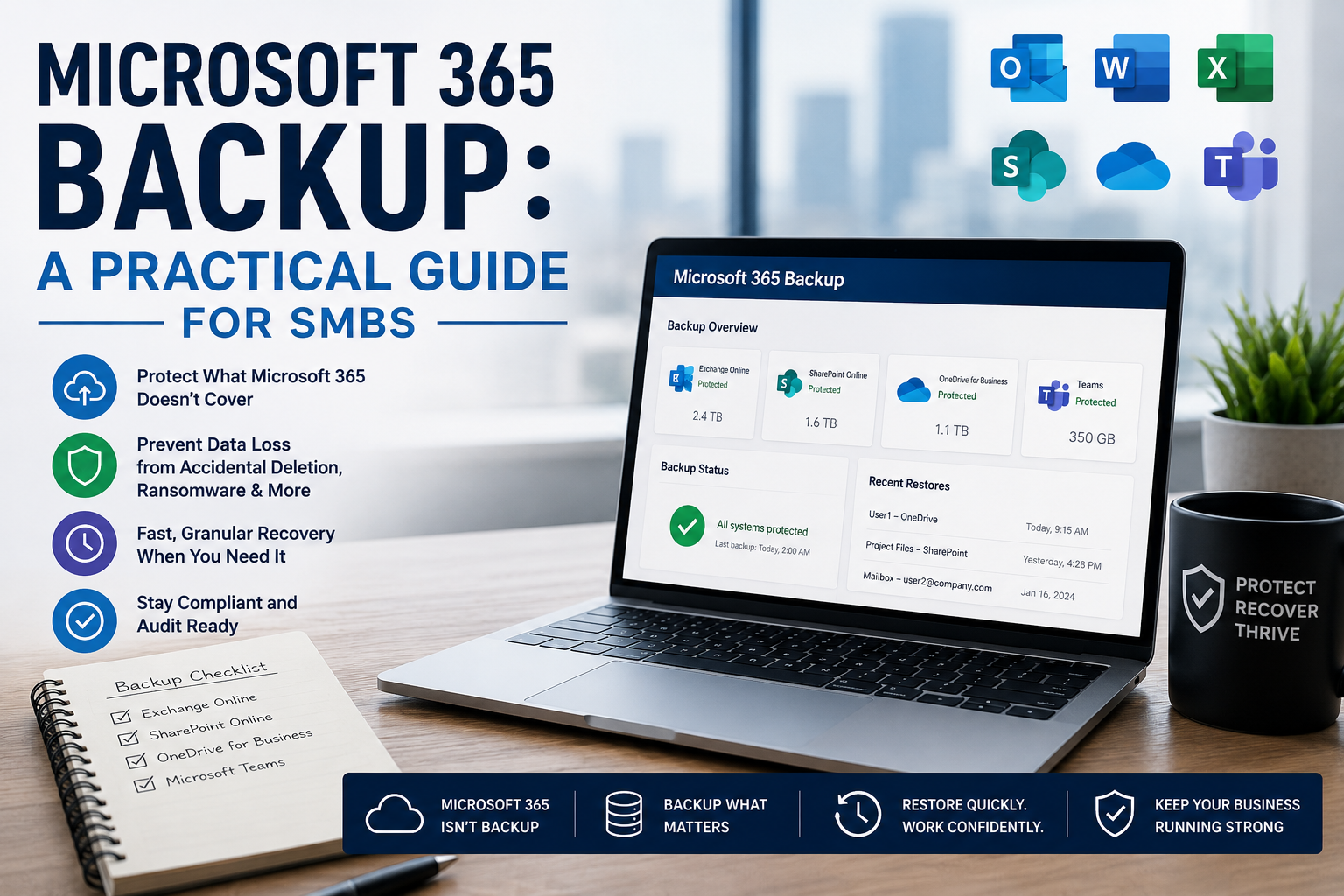
Microsoft 365 Backup: A Practical Guide for SMBs
What Microsoft 365 actually retains and doesn’t, the shared responsibility model that catches most SMBs off guard, and how to choose between Microsoft’s new native backup product and the third-party alternatives.
Microsoft 365 Backup: A Practical Guide for SMBs
What Microsoft 365 actually retains and doesn’t, the shared responsibility model that catches most SMBs off guard, and how to choose between Microsoft’s new native backup product and the third-party alternatives.

Cyber Insurance for Small Business: A Practical Guide
What cyber insurance for small businesses actually covers, what it costs in 2026, and the security controls underwriters now require to qualify for coverage — with a practical guide to evaluating and applying for a policy.

HIPAA Compliance Checklist: A Practical Guide for SMBs
A practical HIPAA compliance checklist for small and mid-sized healthcare practices — administrative, physical, and technical safeguards, plus what auditors actually check and how to catch up if you’re behind.

Incident Response Plan Template: Practical SMB Guide
A copy-paste incident response plan template for small and mid-sized businesses — plus the framework that makes it actually work, industry-specific customization notes, and how to test the plan before you need it.

Managed IT Services Pricing: What It Actually Costs
What managed IT actually costs in 2026 — per-user pricing ranges, what should be in baseline, what’s typically extra, and the red flags to watch for. From a Chicago MSP that’s been quoting these engagements for 20+ years.

“Clean Desk” 2.0: Securing Your Home Office from Physical Data Leaks
In the traditional office, a “Clean Desk” policy was a simple habit: shred the sensitive stuff, lock it away, and don’t leave passwords where someone
The Essential Checklist for Securing Company Laptops at Home
At home, security incidents don’t look like dramatic movie hacks. They look like stepping away from your laptop during a delivery, or leaving it unlocked

The 2026 Guide to Uncovering Unsanctioned Cloud Apps
If you want to uncover unsanctioned cloud apps, don’t begin with a policy. Start with your browser history. The cloud environment most businesses actually use

Stop Ransomware in Its Tracks: A 5-Step Proactive Defense Plan
Ransomware isn’t a jump scare. It’s a slow build. In many cases, it begins days, or even weeks, before encryption, with something mundane, like a
How to Run a “Shadow AI” Audit Without Slowing Down Your Team
It usually starts small. Someone uses an AI tool to refine a difficult email. Someone enables an AI add-on inside a SaaS app because it
Ready for IT That Actually Has Your Back?
Book a free 30-minute IT health check. We’ll talk through your environment, your current setup, and where you stand on security and compliance — no obligation, no sales pressure.
- ✓ 30-minute call, no sales pressure
- ✓ Plain-English breakdown of your IT & security gaps
- ✓ Fixed-price proposal sized to your business
- ✓ Response within 1 business hour
Schedule Your Free IT Health Check
A quick review of your environment and where you stand on security.
